We Deliver Compact Mission Specific Solutions with a Large Impact
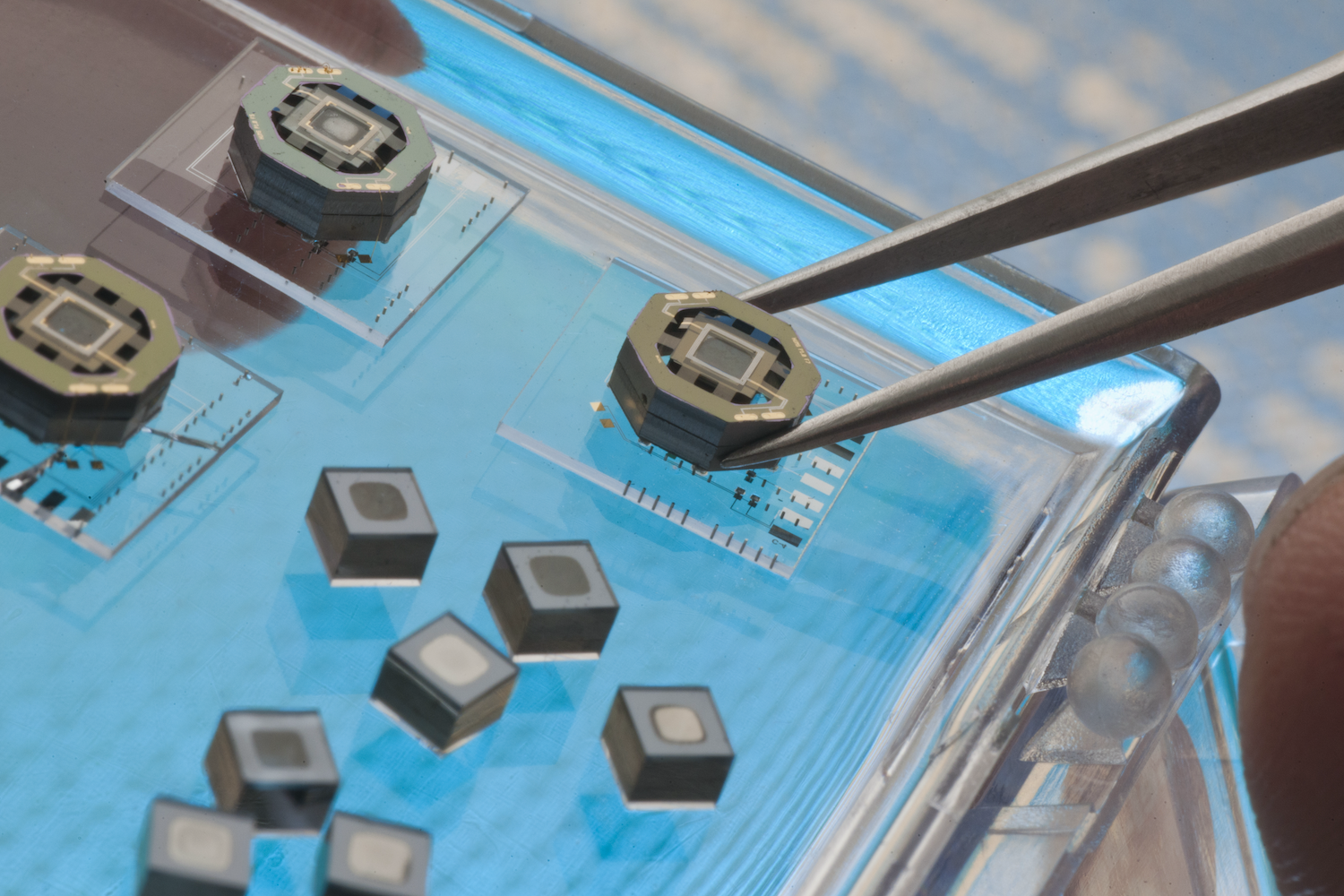
Draper has played a pivotal role in crafting some of the nation's earliest microelectronics, including equipment for NASA's Apollo guidance system and strategic missiles. With this heritage, Draper continues to drive innovation by designing and manufacturing state-of-the-art, mission-specific microelectronics for hostile environments. Whether it is radiation hardening, security, cyber-resiliency, or supply-chain hardening, Draper’s expertise across the entire microelectronics lifecycle ensures that mission-critical processing capabilities meet the demand.
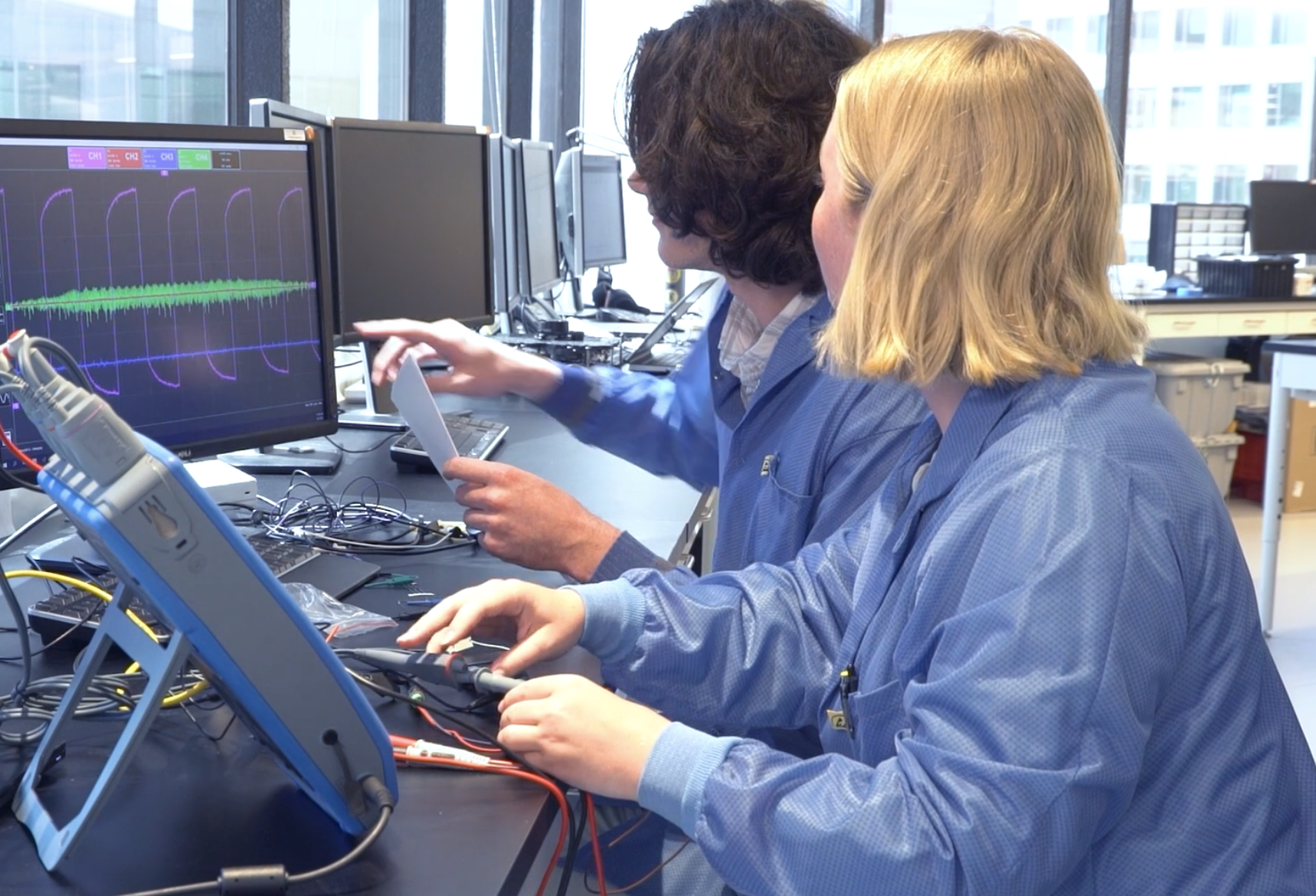
Our skilled team has successfully integrated electronic systems with diverse functionalities, condensing them into compact, singular microelectronic packages tailored to execute mission needs. Understanding that unique missions require the ability to rapidly create solutions for a high mix manufacturing environment, Draper is focused on onshore advanced packaging enabling heterogeneous integration. We are committed to strengthening the domestic microelectronic industrial base enabling trusted solutions for microelectronics fabrication, packaging, and production ensuring USG access to critical components.